The Internet is a deep and multifaceted entity, offering an excessive amount of information, services, and opportunities. However, there is a mysterious realm called the dark web beyond the surface web we can easily access and are commonly familiar with. Here are the 15 Best Dark Web Markets in 2023 that you must visit!
A portion of the internet known as the “dark web” is purposefully hidden and is not accessible through popular search engines like Google and Firefox. It is a nefarious site full of illegal activities and serves as a forum for anonymity, privacy, and uncensored communication.
In this article, we will unveil a step-by-step guide on how to access dark web websites, along with safety precautions and exploring the best deep web browsers.
Let’s start, but make sure to follow all the precautions mentioned while exploring the dark web and prioritize your privacy and security.
What is the Deep Web?
The Deep web is also known as the “invisible web” or “hidden web.” Most people are confused and consider the dark web to be a synonym for the deep web. But, both terms are quite different. You can see the difference between the deep web and the dark web in the later section of this article.
According to research by expert researchers, traditional search engines index only about 1% of the web pages available on a website.
It means 99% of the data is hidden. It is the same as when the iceberg sank the mighty Titanic. The majority of people depend on search engines to get the information they want. As a result, the deep web remains hidden.
Everything you get from the traditional search engines is the clearnet or “Surface Web.” Traditional search engines will be accessing normal browsers such as Chrome, Opera, Safari, Firefox, etc.
Here’s the traditional, clearnet browser list:
- Google Chrome, Firefox, Opera, Safari, etc.
Background History
The term dark and deep web first came out in 2009. Nevertheless, they existed beyond 2009. One of the researchers, Michael K. Bergman, differentiated online searching from dragging a net along the surface of the sea. Obviously, you will get many helpful things. But unfortunately, you can’t catch it all.
Regular search engines won’t index deep web content. In fact, if you encounter the definition of the Deep Web, you will find out that “Content that is not indexed by clearnet search engines.”
Therefore, you need special permission/access, software, and browsers to access them. Search engines do not index your information, such as bank records, school records, adoption records, classified Govt. data, or even basic website dashboards. These are all “Deep web content.”
Now you have a clear idea about the deep web, let’s dig out and explore the dark web.
Overview of the Dark Web
The dark web, or dark net, is a small section of the deep web that is hidden on purpose. In order to access websites and data on the dark web, you need to access a special tool.
Websites that are commonly associated with the dark web are those marketplaces where illegal goods, such as narcotics, firearms, and stolen credit card numbers, are purchased and sold. The most sinister aspect of this web is that they used to exchange child pornography, hire hitmen, and engage in human trafficking.
Furthermore, the dark web carries content and data that can be accessed anonymously. You can use it as a blog, forum, chat room, or private gaming server.
The most amazing charm of dark net websites is anonymity. No one knows the real identity of the user as long as you take the necessary precautions. Thus, users’ identities are safe from governments’ and corporations’ prying eyes.
Journalists and whistleblowers access the dark web and Tor to exchange sensitive information. For example, Ashley Madison posted on a site that was only accessible to Tor users.
Difference Between the Deep Web & Dark Web
The portion of the internet that is not indexed by search engines is known as the deep web. The deep web, on the other hand, has a lot of information, including scientific white papers, medical records, tax-related data, PayPal subscriptions, army communications, and more. The deep web is concealed behind HTTPS forms, but you may readily access its information if you know what you’re looking for.

Most websites hosted on the dark web will be accessed on a credential basis. For instance, if you’re a healthcare provider with a website displaying online blood testing, that particular section will be hosted on the deep web. However, it will never be indexed by Google or Bing and can only be used with a password.
Now comes a question in your mind what is the dark web? If the surface web is, Google’s BFF and the deep web is its secret lover. Well! The dark web will be their evil twin.
According to researchers, the dark web is a mixture; it is a rendezvous place for drug dealers, black hat hackers, hitmen, and human traffickers on one side. On the other hand, it is a place where people submit anonymous tips (whistleblowers).
Consequently, both parties prefer the dark web since it can make anything and everyone invisible. Privacy and anonymity are the core values of the darknet. You can access it through onion-type links.
Then, What is the Surface Web?
The surface web is also known as the “visible web” and is the part of the web easily accessible to the general public. It is indexed in standard web search engines such as Google, Bing, and Yahoo.
Generally, any reference to the visible web will come from common websites with a familiar internet domain extension.
Top-level domain (TLD) is another word for domain. However, it is the last part of an internet domain name, expressed after the last dot. For instance, Google.com and deepweb.com both belong to the “.com” top-level domain.
Therefore, websites containing domain extensions like.com ,.org,.net,.biz,.info, etc., will be found on the surface web. Additionally, the content of the pages won’t require any special or custom configuration to access.
It was stated by Search Engine Land in 2013 “they knew about 30 trillion pages,” as said by Google. In 2016, Google indexed an astonishing 130 trillion individual pages, and the number goes on and on. This was Google’s latest official update on how many pages are in their database.
According to a report from October 2022, the total number of pages Google has indexed is approximately 58 billion individual pages.
In a nutshell, only 0.024% of all the known pages are searchable in Google’s search engine.
Safety Precautions While Browsing the Dark Web Websites

Step 1: Plan Ahead
There are various reasons companies and individuals want to access the Dark Web. SMBs and enterprise companies want to access Dark Web portals for stolen corporate account information. Individuals might want to monitor sites for evidence of identity theft. Here are the key takeaways to consider:
- Must set a goal, make plans, and stay focused. Keep in mind that you must know what information you’re looking for and why you’re logging on to the encrypted web. For instance, if you are a reporter, focus on PGP, email, and encrypted communication. If you’re searching for credit card information, go for the Silk Road-type markets.
- Get what you want, securely disconnect TOR and Tails, then log off.
Step 2: Obtain a New USB Flash Drive
Go and buy a new 8 GB or larger USB flash drive. Remember to use a fresh and unused drive. You can install Tails and Tails directly on your storage device.
Step 3: Prepare Your Local Machine
Most people probably use a fresh laptop. But if you can’t, do everything to secure and isolate mission-critical information.
- Back up your critical data and local files.
- Ensure your hardware is optimized and malware-free.
Step 4: Download Tails and TOR
Download TOR and Tails, which are available on the TOR Project website. You can directly go to www.torproject.org, insert your USB drive, and follow the instructions on tails.boum.org.
Step 5: Browse Safely
Here’re the most common search engines:
- DuckDuckGo
- The Hidden Wiki
- Onion.link
- Ahmia.fi
- Grams
- Torch
However, encryption is strong but not impenetrable. The FBI discovered and took advantage of vulnerabilities in the TOR network. Although the agency denied revealing the source code used to penetrate the network, law enforcement agencies monitor the world and operate on the Deep Web. Thus, TOR’s project members vowed to patch network holes and strengthen the protocol.
How to Access the Dark Web
The Dark Web is decentralized, meaning the data is stored on many different servers worldwide. Most users on the dark web access the Tor (The Onion Router) browser. A large number of URLs have domain endings such as “.onion,” meaning the URLs are only accessible by Tor users.
Moreover, the Tor browser is available for Windows, macOS, and Linux operating systems.
Here’s how to get into the Tor network; follow these easy steps as mentioned below.
1. Install a Reliable VPN
Installing a speedy VPN (Virtual Private Network) when accessing the dark web is important to protect your privacy and anonymity.
The dark web is designed to do things anonymously, but it is possible only when you take action to maintain your privacy. It is secure and takes your privacy seriously when browsing marketplaces on the dark web. However, nothing good or legal has been sold on dark web websites, while you may find legal stuff on Amazon.
There are two organizations that track Tor users: ISPs (Internet Service Providers) and the FBI. This is not the case with all Tor users. Your Internet Service Providers are unable to see which websites you are visiting on the dark web when you are using Tor. But, they will recognize that you are accessing the Tor browser if they analyze your monitored internet traffic.
However, they are unable to see any of the content you are reading or what you are sending and receiving through the Tor network.
Once you install a VPN, all your activities will be hidden on the dark web from unwanted snoops from your ISP or the FBI. Furthermore, the VPN is an extra layer of protection on top of Tor’s network protection.
It means that when Tor is compromised, or perhaps there’s a new vulnerability exploited in the Tor network, a VPN will secure your privacy. The compromised Tor exploit may be traced back to you, but your VPN will lead it somewhere else, which is impossible to trace back to you.
Therefore, VPNs protect you from hackers who might be after your personal information or payment details. However, hackers are the biggest problem on the Dark Web websites.
Key Points to Consider While Choosing the Best VPN
| It is important that your VPN does not keep any kind of log. |
| The VPN must be compatible with the Tor browser. |
| Your VPN must be speedy and fast in progress. |
2. Download the Tor Browser
Accessing the dark web with a regular browser like Chrome or Safari is impossible. Besides, you must use the Tor browser to access the dark web. Keep in mind that you need to download the Tor file. You can access it on their official website.
Before going to download the Tor browser, make sure to activate your VPN first!
So, when you activate your VPN, it means that your privacy is secured. Now, visit Tor’s official download page.
Then, simply select the operating system you are accessing and download the file. The website provides downloads for macOS, Windows, Linus, and Android. However, an iOS version of the official Tor browser is not available. But there are other Tor browser alternatives available in the App Store.
3. Install the Tor Browser
After downloading, it’s time to install the Tor browser on your device. There are different installation instructions for macOS and Windows. All you need to do is double-click the downloaded file in your download folder.
Windows users will install the app easily. All they need to do is follow the prompts in order to install the app. On the other hand, macOS users need to drag and drop the Tor Browser icon to the Applications folder. You can even do it within the window that opened when you double-clicked the downloaded file.
Install the Tor Browser For Mac Users:
You cannot access the “Tor Browser” if you turn off installations by unidentified developers. Here’s how to do it:
- Visit System Preferences.
- Tap on “Security & Privacy.”
- Select “Open Anyway” at the bottom of the page.
- A confirmation pop-up will display on your screen. Click on “Open.”
4. Start the Tor Browser
It’s time to start using the Tor browser. You need to just double-click on “Start Tor Browser” -for Windows or “TorBrowser” -for Mac users.
Hence, the Tor browser will open in a browser window. Now, you are ready to enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains.
Which Services and Tools Are Available to Access on the Dark Web?
Many services and tools are available on the dark web, many of which will be used for villainous purposes. However, some of them are relatively harmless services.
Various search engines on the dark web can help you find what you are looking for. One of the best examples is DuckDuckGo’s no-track dark web search service, which can be accessed in the Tor browser and is an amazing resource for information about the dark web. Other dark web search engines such as Not Evil, Torch, Haystack, and Ahmia.
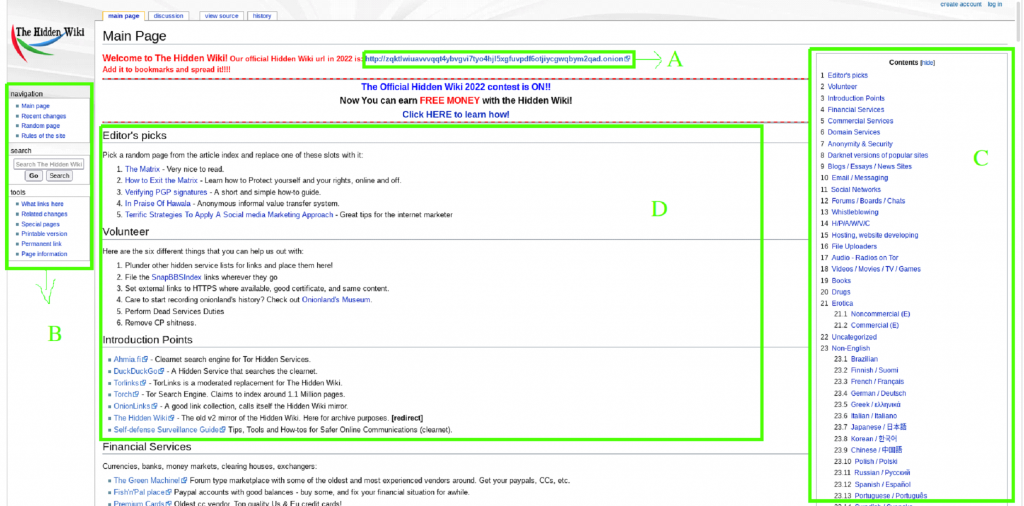
Moreover, the “Hidden Wiki” can be accessed in a normal browser, which provides a bulk of dark web links, but most of the links have dangerous websites. So be careful when accessing those links in your browser.
Being villainous services and tools, they can easily be available on the dark web. Furthermore, Ransomware is also available on the dark web, where users can purchase scripts, code, and other tools that will be used to perform encryption of other users’ data, allowing them to hold the data of bad actors with less experience for ransom.
| Overview of Ransomware: Ransomware is malicious software that encrypts or blocks access to the data stored on a user’s computer or mobile device. Then, the victim asks to pay “ransom” to unlock files so that they can access them once again. |
First, data gathered from ransomware and data breaches is available on the dark web. Millions of customers’ personal data includes their names, addresses, bank account and credit card information, and many other forms of sensitive data.
Additionally, there is various information available on the dark web, such as business operational data, including financial data, intellectual property, and trade secrets.
More Facilities are Given by Darknet Markets
It offers transactions for illegal goods and services. The first dark web marketplace was the Silk Road, which allowed users to trade multiple types of nefarious goods and services, including weapons and identity fraud resources. On the other hand, many authorities have shut down dark marketplaces, but new markets will soon appear in their place.
Hackers sold their services on the dark web. Hackers will offer services against banks and other financial institutions on the dark web. Moreover, it has been calculated that a large percentage of dark web traffic is related to illegal pornography, including underage victims.
Best Deep Web Browsers

If the Tor browser is not working on your device, try any of the Tor Browser alternatives mentioned below to access the dark web.
Here you go!
1. Freenet
It is one of the best alternatives to the Tor browser. If you’re searching for top-notch data encryption, you must try Freenet.
Compared to insecure browsers, Freenet lacks a central server, which makes it easy to hack into. You can use both clear net and dark net using this browser.
No one can access it except the person who uploads the data. Therefore, your data remains secure and safe.
If your TOR browser doesn’t work, then we will recommend that you use Freenet right away.
2. I2P
If you have been searching in the dark for a long time, you may have heard about I2P. You will be lost in the unstoppable debate if you want to compare Tor and I2P.
The most amazing thing about I2P is that it secures data in different layers, making it difficult for invaders to hop in. In short, you can say I2P is the internet within the internet. It can be accessed with both public and private keys.
Moreover, you can trust it with maximum credibility. If you choose I2P, I must say you won’t regret it.
3. Whonix
It is more than a browser; Whonix is a Linux distribution that offers the best in terms of security. Hence, there are various security professionals who access this Linux destro. Generally, it runs on the Tor framework. You can also download an isolated version. Here’s how you can install Whonix Dark web.
Whonix is the best free alternative to the Tor browser, and it can’t troubleshoot you for downloading and installing. The two versions are Whonix-gateway and Whonix-workstation. Keep in mind that the first one solely relies upon the Tor, while the second one is isolated. When you start using it, you will recognize that it won’t steal your information.
Thus, you have read the top 3 alternatives to the Tor browser. But if you ask me which one is the best, I highly recommend Tor as the best deep web browser.
Conclusion: Access the Dark Web
The dark web is a hidden realm within the vast expanse of the internet. At the same time, it contains a heinous and notorious reputation for illegal activities and serves as a platform for privacy, anonymity, and unrestricted communication.
You can easily and safely access the dark web with the help of practice, research, and prioritizing personal security. Make sure to look at your jurisdiction’s laws and exercise caution to secure your online experience.
| Reminder: Using dark web websites requires precautions, knowledge, and the use of specialized software like the Tor browser. |