Hundreds of billions of accounts are negotiated every year in data breaches via phishing, malware, and other type of techniques. This data breach happens when hackers crack a password, and an account is then vacant on hacker forums and marketplaces on the dark web and deep web.
Hackers have made it a tradition to use several means to hack and crack their victim’s account, which is known as password cracking. So, do you know about password cracking? If not then you are at the right spot.
In this post, we have mentioned all the details about password cracking, techniques that are used to crack a password on the deep web and dark web, and some communities and groups on the deep web and dark web that provide services to crack a password. Let us dive into the post without any delay.
What is Password Cracking?
Password cracking is basically a process of regaining the passwords from a device or data it transmits. It does not require a complex or advanced method. A hacker can straightforwardly extract passwords from all the probable combinations with a simple physical force attack.
However, the skill to crack a password is the most enjoyable hack for bad actors in the deep web and dark web. It raises the sense of search and is valuable in figuring out the password. The password cracking may not have a red-hot wish to hack the password of everyone.
However, the actual password of the user is not kept in the well-made password-based verification system. That is why hackers can easily access to user’s account on the system. As an alternative to a password, a password hash is kept by the verification system.
The hash function is a one-way encryption cipher design. Its revenue that it is problematic for a hacker to get the input that makes a given output. The comparison of the real password and the comparison of 2 password hash are nearly good. The hash function compares the kept password and the hash password offered by the user.
While it is quite easy to crack a password, it would take a botnet or GPU to try a series of passwords rapidly. That is why most password hash function uses key-elongating algorithms. They help to increase the time and resources it would require to service a physical force attack.
9 Techniques Used to Crack a Password on Deep Web
Password cracking does not really require any complicated high-technology methods. Hackers frequently prefer to employ the easiest password-cracking technique. The easiest method is a social engineering-based method. We (humans) are perhaps weak links to their password security. However, hackers know that and depend on targeting victims to gain access to their passwords.
But if this method is not successful, then the hacker chooses a different approach, which is a more complex computing technique. However, you can easily protect against hackers by using key stretching software for your personal and financial passwords.
Below, we have mentioned a detailed list of techniques that are used to crack a password on deep web marketplaces.
1. Social Engineering Attack
Social engineering technique to crack a password depends on user unwariness and do not always need a chic tool. If users are not careful, then the hackers often try to get data, engaging them about specific details that might feed the hacking procedure. The hackers can call it a Google negotiator or a bank representative, and whereas this does not need much software, it is unexpectedly effective.
2. Speculating
Speculating is another technique to crack a password used in the deep web and dark web. It contains some form of data sourcing from well-known companies. It is such that the attacker may not need any progressive computing means, just good speculations.
So, it is recommended to make your password harder to guess by swapping from sluggish, repetitive, pathetic passwords. Also, you should use less memorable words and phrases for passwords, including names of pets, vacation places, lovers, sibling date of birth, etc.
Here, we have mentioned some common passwords that are really easy to speculate and crack.
- Password
- 123456789
- 1q2w3e
- Qwerty
- Qwerty123
- 111111
3. Malware Attack
Malware technique to crack a password depends on the innocence of the user and is frequently operative. This technique to crack a password has three main types.
- Key Loggers: This procedure records your keyboard strokes and sends the data to the hackers.
- Screen Scrappers: It can effectively take screenshots of your screen as you type and send them to the hackers.
- Backdoor Trojan: It can unlock the system and grant the hacker complete access. They are hidden on skip ads or malicious download buttons.
4. Phishing Attack
Phishing technique is the most common method used on the deep web to crack a password. It basically entails tricking the user into clicking on a link or mail attachment containing malware. This method works when installing an urgency in the mail recipient. The user believes the mail or link; once they click on the link, the password-cracking software gets installed in their system. The user will be conveyed to a replica site where their credentials will be kept.
However, phishing has different kinds that depend on the situation it is required for. Here, we have shared some most common phishing techniques to crack a password.
- Whaling Phishing: The hacker aims at high-ranking or senior-ranking execs and exploits company-specific data for the attack. This data can be a letter from a stockholder, a customer review, or a criticism.
- Spear Phishing: It targets a specific person and tries to gather as many private details as possible before the attack.
- Voice Phishing: The hacker sends a fake text from a financial organization, like a bank. Ask the user to call a fake customer service to enter private data.
5. Offline Cracking
Offline cracking is a safer option for hackers that lets them take the hashed passwords offline and attempt to crack them more professionally and safely. Here, the safety is that online hacking is straightforwardly visible and thus escapable. When hackers attempt to crack the password of an account online, they can activate a lockout owed to too many attempts.
However, offline cracking includes taking hashed passwords right from a database using SQL injection. The next logical consequence is administrator rights; if the hacker gets this, that is the victory.
6. Brute Force
The brute force technique for cracking passwords is also known as dictionary attacks. This attack is a final effort when all other password-cracking techniques have been futile. It contains trying every single probable blend until one of them works. This method is time-consuming without the exact information.
However, it will check if the user password is not a usually used phrase like I love cats by running a check via the dictionary. The dictionary will also contain leaked passwords from other accounts to help confine the probabilities of what the actual password might be. Suppose the user selects a strong password that is one word instead of a phrase. The success of these compact attacks would be increased.
With precise cracking tools, the hacker can cut the time required to run all the possible blends. These tools will feed the customer habits or fringe information into the system for more updated options. The practice is known as “credential stuffing” and can aid hackers save your password much quicker.
It is recommended to use a password generator and manager so your password options are much harder to interpret. But if you do not have either, you can use a lengthy phrase holding up to 5 characters.
7. Spidering
The spidering technique is pretty identical to credential stuffing and a part of brute force. It involves gathering relevant data about the victim. The assumption is that the victim would use familiar data in their account as with their password creation.
Moreover, this technique helps create a list the hacker can have that cuts the time to crack a password. Once the hacker, with the support of the tool, concludes the check on the victim, its social media, and other related sources, the list should look a little like this:
- Victim’s name
- Victim’s DOB
- Address
- Victim’s sister
- Victim’s siblings
- Purpose of account creation
Now, all that is port is alimentation this data into a strong password-cracking tool, buzz back, and get the consequences.
8. Mask Attack
Another technique to crack a password used in the deep web and dark web is a mask attack. It adds a part of the password the hacker may already know. For instance, if the hacker can know how long the password is then they can filter their attack parameters. However, a mask attacks deadly if you are not adequately protected. The range of attack lets it filter for specific words, special characters, specific number ranges, and just about any other detail the hacker can think up. If any of the required data is leaked, it means a whole breach.
9. Rainbow Table
In the rainbow table attack technique to crack a password, a hacker stores a previously cracked password along with common passwords. They are arranged in what is known as a rainbow table, which makes the password-cracking procedure easier and more effective. It contains all the probable passwords means that the table would be worth hundreds of GBs of data.
While bulky means the table has a fairly infinite supply of passwords for its cracking procedure. The hacker also needs a password management tool for salting and key stretching.
Salting is so effective that if large enough (from 128-bit and above), two users can use a similar password but have exclusive hashes. Consequently, anyone trying to crack either password would have a hard time doing so. With “key stretching,” the function fluctuates, as it proposes to raise the time for hashing and significantly decreases the number of times the hacker can try to crack within a given time.
Unveiling Password Cracking Communities and Groups on the Deep Web
Hacking or password-cracking communities on the deep web and dark web is very high. However, these communities are closed to the public; to join the discussion, you have to request an invitation. They specialize in topics like social media hacking, data theft, malware, and exploits and hit and run attacks.
Here are some famous examples of password-cracking communities according to security companies and cyber experts.
- Hackforum
- Torjanforge
- Mazafaka
- Dark0de
- TheRealDeal
- Underground Hacker Markets
According to researchers, there is a growing interest in the personal data of any kind that is used as a second form of authentication is alive and well in Deep web forums and communities. These markets are booming with counterfeit documents to enable fraud further.
In addition to the fraudulent activities, these markets also offer hacking tutorials. These hacking tutorials offer instructions to criminals and hackers who want to enter into the business of stolen credit card data or data on running exploit kits for the firms of spam and phishing campaigns and tutorials on how to organize hit-and-run DDoS attacks. Other tutorials offered in these hacking communities include how-to guides to hack ATMs and to manage a network of money mules, which are the principal actors for the cash-out procedure of every illegal activity.
So, it is apparent that the underground hackers’ communities in the deep web and dark web are monetizing every piece of data and can steal or buy and continually add services. Therefore, other scammers can successfully carry out online and in-person scams.
Services of Crack Password on Deep Web
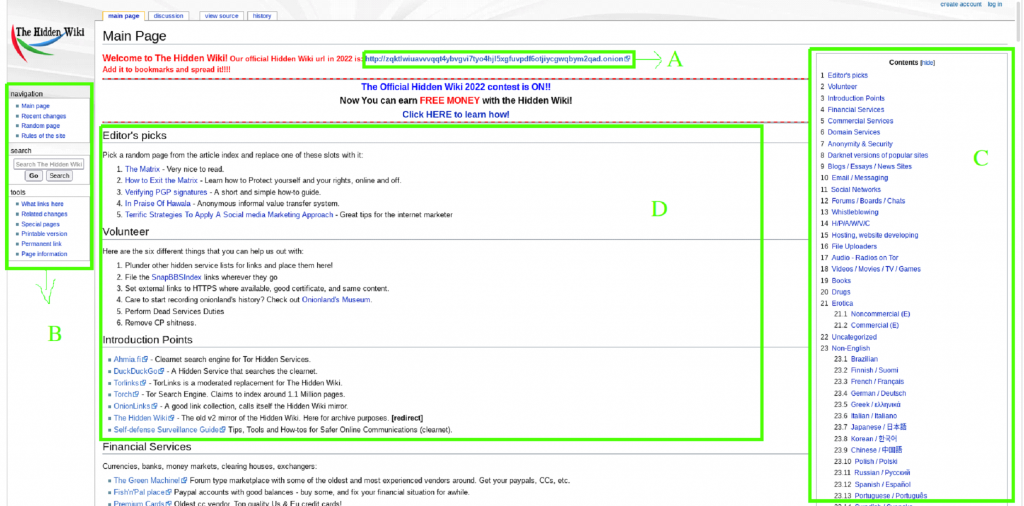
There are many ways to get the password crack or hacking services. However, the most interesting place to meet the members of principal hacking communities is the Deep web. Hacking and password cracking services are the most attractive cargoes in deep web and dark web marketplaces. It is really possible to hire a hacker to request to crack the password of a Gmail social media account for cyber-surveillance determination.
Here, we have mentioned the password cracking and hacking service on the Deep web.
- According to the reports on the deep web, if an individual wants to hack someone’s Gmail account will have to pay about $90.
- On the deep web, hackers can also crack The WordPress-built website for 2k euros.
- Hackers could be hired to crack social media accounts. The cost to crack the password of someone’s Facebook account is $350 in the deep web marketplace.
- Hackers can also steal someone’s Hilton points for just $15 or compromise a Netflix account for just $1.25.