Are you curious to know about the Facebook Dark web? Luckily, this post is like diving into a paradise for you.
Facebook’s administrator has released a feature for its user to join dark web via anonymizing service Tor browser. The encrypted data lead hackers to expose and trade personal and financial data.
However, some agencies and companies that use the dark web must keep their anonymity to analyze foreign security stations. They use this service for the benefit of their nation. Meanwhile, a massive number of people use the dark web for their illegal and criminal work, which is actually illegal and criminal activity.
In this detailed guide, we have instructed our readers on how they can use FB on the Dark web. And know the detail of Facebook leak data. We also share some methods users can apply when, unfortunately, their personal and financial data is exposed in cyberspace.
Warning: We warn you not to use this information below for illegal or criminal activities.
About Facebook Dark Web
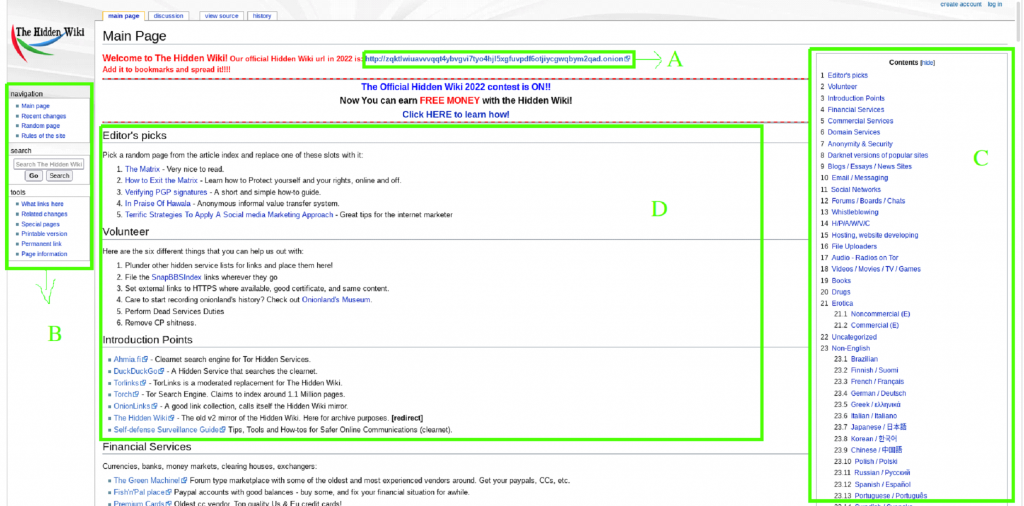
Facebook directorial stated on October 2014 that its users could connect to the FB site via a privacy-protecting Tor browser and encode the data using HTTPS. The Dark web FB’s onion address allows users to access FB through Tor without trailing the cryptographic protections delivered by the Tor browser. Moreover, it delivers end-to-end communication from the browser directly into a Facebook data center.
The number of users who got into Fb via the Dark web in 2015 was about 525000 people monthly. In April 2016, the app was used by over 1 million users monthly worldwide to get stuff on the dark web. According to a news report, the users of Facebook via Tor include nonconformists who try to avoid censorship, criminals, and United States government staffs who require analysis from the overseas security service station.
But Facebook’s directorial states that they launch site on the Dark web to users who already access its services via Tor but block by its program’s security panels. In countries like China, North Korea, Iran, Cuba, and others, government authorities block Fb access through the dark web to prevent access to the site. In such countries, the public appeal to their government to block the restrictions.
How to Open Dark Web Facebook
When you want that, your internet provider will not access to recognize that you logged in to social media site like Facebook. You must log in to Facebook via the Tor onion address. After you log in to your Facebook account, the server will continue monitoring your activities.
Below are the steps you can follow to log in to Facebook using the Tor browser.
- First of all, open your computer device.
- Then install the Tor browser to access the network.
- Open the Tor browser when it is installed on your desktop device.
- Enter the onion site link of Facebook at the search bar that you see on the homepage of Tor.
- After the Facebook page is loaded, then verify that you are at the official site of Tor Facebook.
- To verify, click on the green deadbolt that you see in the address bar.
- After that, you will see DigiCert Inc on your screen. That shows you are at the right place.
- Now you are able to use your FB account on the dark web via the Tor browser. That’s it.
Tips to Remember When Using Facebook on the Dark Web
- Users can access the Tor network from the USB flash drive because it has a binary format that can operate from USB.
- When you install the Tor browser, keep it up to date, as the network usually keeps its newer versions posted.
- Users need to show a bit of patience and remain to keep calm because Tor is fairly slow compared to a normal browser.
- Always make sure that you deactivate the HTML5 canvas because it can get used to tracking your browser.
- Users can also access the Tor browser to use the VPN if they want to upsurge the level of security.
- Keep in mind that the server will monitor your activities when you log in to your Facebook account.
Reason Why folks Want to Access Facebook on Dark Web

People mainly select the Dark web (Tor browser) to communicate from the Fb server because they find this safer and more secure. It will be continued to be a success because there are a lot of people who choose this method to open their Facebook accounts.
Facebook Tor website plans to be approachable for extensive connections and similarly offers an additional coating of security to running the Tor browser. This means that all data encodes and Tor users do not lead astray for hacking the accounts. Users can access FB from the dark web without losing the cryptographic fortifications.
When users use the Fb platform on the dark web, the Tor browser cautioned them about nasty exit nodes. These nodes can sometimes be used to detect their unencoded traffic or shred the encryption left. However, the traffic does not leave the Tor network until it is safely inside the Facebook infrastructure when both the user and Facebook are running on the Tor browser.
Break the Tracking System
Using an Fb server on the dark web via a Tor browser network allows people to go to web pages without tracking. Users can view sites whose contents would not reveal in search engines. For those users who want to stop their location and browsing behaviors from stalking. Facebook’s official support for Tor would become popular among them.
Meanwhile, it is fairly difficult to use Facebook completely anonymously. Users who want to access FB on the dark web still require login and authorization. But if users just tell Facebook their name, it does not mean they can find out your location and browsing ways. Actually, the Tor network slightly loses the point unless you just read the information from a page.
Consequently, it is all revenue that users do not have much protection from management. But it prevents Facebook from recording IP addresses and makes tracing users harder.
Safety Blockage
As we know, Tor Browser is a network that anonymous a user’s identity, and it does this by routing internet traffic through numerous IP addresses. Which makes it difficult to trace where the user is browsing from. But when a user gets into Facebook, the situation is not like that. The site makes dodge restriction and investigates that arises much closer to the users’ own connection.
When the site security measures are if a user tries to log in from an unexpected location. It will pennon this as a signal the account has probably been negotiating. It means that users must go through additional security steps, like naming people in pictures before logging overseas.
In the meantime, the Tor browser projects perception is that if a user appears on their system, which is connecting from Australia at a flash may, the next appears to be in Switzerland. So consequently, the Facebook accounts on Tor have activated users since they appear to log in from weird IP addresses all over the world, which is normal in the Tor network.
Millions of Facebook Users’ Data Leak on Dark Web
As per the information, news agencies started printing the reports from Saturday, April 3, 2021. That exposed the Facebook leak data specification, which includes almost 533 million users of 106 countries’ records and is available for just $3.
The leaked data from the Fb server, unrestricted and available on the dark web site, included email addresses, usernames, phone numbers, relationship statuses, locations, and personal information.
According to a cyber threat intelligence security report, they had made a hasty analysis of this stolen data. They state that a dark web user publicizes the availability of the data for purchasing, and the profile photo looks anime-style.
The stolen data was taken in 2019. Cyber offenders still treasure it because the dark web is basically a gigantic marketplace for procuring and retailing personal archives and personal information.
Furthermore, as per the news reports comeback of this leaked data stated that the leaked data of Facebook is still available on the dark web forum. Therefore, after three years, this old leaked data is very vulnerable to massive hacking once stolen.
How Hackers Use Leak Data of Facebook?

At first, the data broker (hacker) groups of the Dark web retailed and traded the dataset. The offenders will use the data from these groups for the conceivable forthcoming. This data contains a large number of rows and many of the PII comprising columns that the users cannot straightforwardly change.
The offenders revealed their method before making the dataset available to the public. Plus, the worth of PII contains in this data helps offenders in various ways. In simple words, hackers already use this data to aim at specific Facebook accounts and find their PII to style their outbreaks effectively.
The phone number is an important factor in our daily lives because we use it for two-factor authentication for SMS or to identify over selves with banks, medical accounts, or social media accounts. Every Facebook user like you and I has used the personal phone number for certification.
Many users do not easily change phone numbers on any social media account. This is the fact that we examine the following high impact of the leaked data used by hackers.
Doxing of Prey
Hackers can center from the Facebook ID to a phone number when a hacker gets access to your ID. Accordingly, doxing (publication of personal details like location and phone number) may lead to harassment of private people and can make stronger physical harm.
Switch the SIM
People who used to know how to swap sims without difficulty targeted the customers of Bitcoin services, interactions, and securities firms. Luckily this leaked data is like Christmas for them. Sim switchers will use the information as a tool to target account takeover for the purpose of scams and harassment, and other illegal activities.
Facebook Accounts Takeover from Dark Web
The SIM switch is central to the account takeover. The leaked data can also intensify the effectiveness of social media account takeover ways. Because the leaked data include gender, employment position, location, name, and other personal information.
This personal information is enough to reveal the security questions of a person. However, informally engineer service sustenance councils or servers as further pivot opinions to discover more data.
Spam and Spoofing
According to a news report, SMS phishing strategies have increased during the pandemic. They also highlight their worth. This highlighted leak avail list of victims and probably used to blowout malware, spam, and spoofing occurrence, which is a leak by hackers. The dataset is a part of nations that let the hackers use it to modify their targeting strategies according to the location.
What to Do If Your Facebook Data Is Exposed on the Dark Web
In 2021 social media, more than 150 million users’ personal data is outflow on the dark web. That sensitive data uncovered passwords, IP addresses, email addresses, financial data, gender, personal identity, and phone numbers. And other personal information of social media users.
As a result, criminals or hackers might try logging into that exposed account using the password. However, if you encounter a data breach, there are some methods you can take to recover control of your accounts and secure your personal information.
Discover What Data is Exposed
You must figure out exactly what information was exposed in the leaked data. Some server will contact their users to know your personal information was discovered in a data breach.
You can search the data breach sites to see if your social media (Facebook) information has to negotiate on the Dark web.
Delete your Home Address
When you see your home address in the leak data. Which posts on other sites, so you can report it and remove it. Report it to Google and Bing web search. It can help you to remove your address from their search engines.
- On Facebook, select the post that you want to report. Then click on the three dots and click on the find support or report post option. Then choose any suitable option.
- On Reddit, select the post and click on the report option that you see next to the post.
- On Twitter, tap on the file a report that states personal information was posted.
Keep in mind that it is not probable to delete your home address from the entire web; it connects to public records. However, you can delete your home address from online sites via paid services like DeleteMe.
Change your Passwords
When your password is transferring, you have to change it not only from that social media server. But also, everywhere else, you insert that password. To do this, you can use a password manager to store complex passwords for every account.
Switch your Account to Multifactor Authentication
Hackers can probably log in to your social media accounts like Facebook when your personal phone number is on dark web data breach sites. In that case, switch all your accounts into multifactor authentication MFA. When you apply this technique, you will require a second factor to add your passcode to log in.
Though if a hacker gets your password, they still would be unable to get into your account. Meanwhile, some servers don’t let you use the authentication or hardware keys for MFA. In these circumstances, we recommend you get a Google Voice number for any account. That requires you to use a phone number as additional authentication.
Delete Accounts you are Not Using
If you have too many accounts, can intensify the risk of the data being stolen and outflowing. That’s why you need to get rid of the accounts you have not used for a long time. Or those accounts that you are not using.
Restrict you Credits
If you determine that your social media safety numbers or financial data leak on the dark web or elsewhere. You have to freeze your credit, limiting access to your credits. It makes complexity for hackers to open new accounts in your name or information. To do this, you can contact credit agencies, for example, Experian and TransUnion.
In certain situations, you will have to buzz the freeze provisionally. For instance, when you are put on for a credit card loan or rent a flat.
If you took the steps mentioned above. Be sure to look at all your active accounts, including social media and financial related.
Summing Up
Facebook has released its service where users can get into their Facebook account from the dark web. That can run the anonymity software Tor onion. This tor browser recoils users’ connectivity via three additional encrypted random computers around cyberspace. That makes it harder for any network detective to perceive the traffic to track their source.
Due to these features of the Dark web help, hackers trade the leaked data of Fb servers and other social media accounts. Here in this post, we have shared detailed instructions on how to use Fb on the dark web with an audience. And what they can do when encountering that their data is exposing.
So, let us know in the comment box if you have any queries.